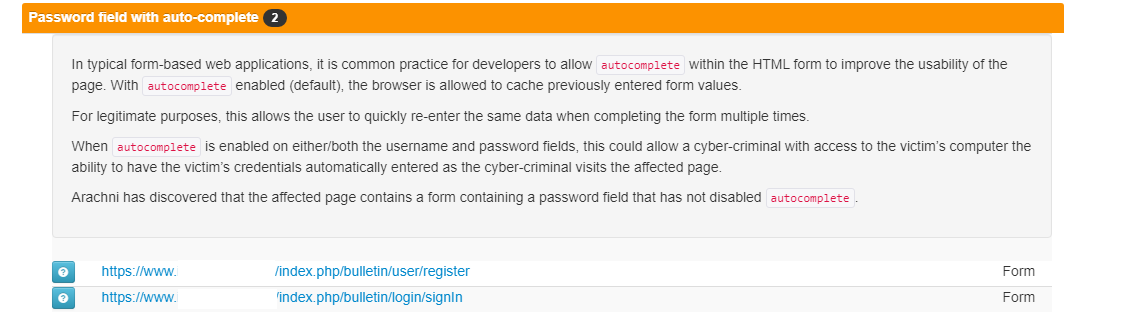
I would like to suggest that proper autocomplete attribute tags be added to the sign-in and registration forms in OJS. One cue is that Chromium now provides the following in the console when visiting an OJS journal:
[DOM] Input elements should have autocomplete attributes (suggested: "current-password"): (More info: https://goo.gl/9p2vKq)
<input type="password" class="form-control" name="password" id="passwordModal" value maxlength="32" required>
The practice of adding machine-readable autocomplete tags (such as for the username and new/current password fields) makes the platform more accessible and following best practices. This allows the browser to support the user in creating a more secure password and saving it.
For example, I’ve added the current-password tag to the end of this input. This tells the browser that this is a current password instead of a new password. Simple enough.
<input type="password" class="form-control" name="password" id="passwordModal" value maxlength="32" required autocomplete="current-password">
The power then rests with the user if they wish to disable browser-based autocomplete at the client side. Right now, the fields aren’t properly tagged so you get irrelevant suggestions. Please see below for resources from the Chromium project on this matter. I’m curious to hear if there are any reasons why these attributes weren’t added so far, or if they could be added in the future. I could also submit a pull request if this is preferable.
https://web.dev/sign-in-form-best-practices/
https://www.chromium.org/developers/design-documents/create-amazing-password-forms